OSPF Neighbor Sim
[am4show have=’p2;’]
Premium Member: You can practice this sim with our simulator via this link.
[/am4show]
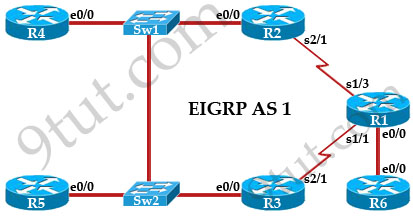
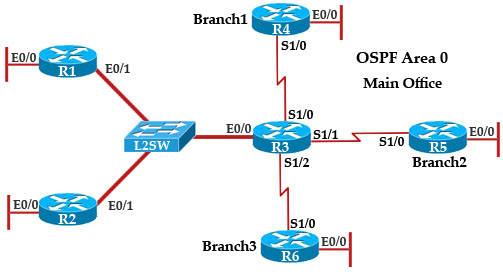
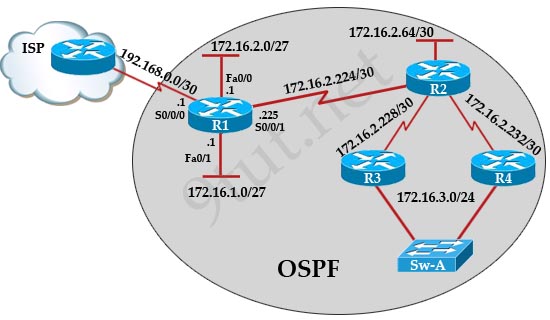
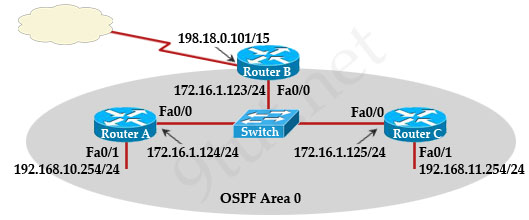
The topology below is running OSPF. You are required to troubleshoot and resolve the OSPF issues between the various routers. Use the appropriate show commands to troubleshoot the issues.
Topology:
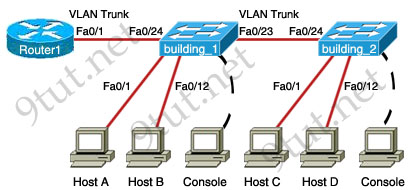
VTP Configuration Sim
Question
[am4show have=’p2;’]A new switch is being added to our LAN. Complete the following steps:
+ Configuring the building_2 switch with an IP address and default gateway.
+ Use the last available IP address on the management subnet for the switch host address.
+ In addition, the switch needs to be configured to be in the same VTP domain as the building_1 switch and also needs to be configured as a VTP client.
+ Assume that the IP configuration and VTP configuration on building_1 are complete and correct.
The configuration of the router is not accessible for this exercise. You must accomplish the following tasks:
Determine and configure the IP host address of the new switch.
Determine and configure the default gateway of the new switch.
Determine and configure the correct VTP domain name for the new switch.
Configure the new switch as a VTP client.
Note: You might be asked to use first, second… available IP address on the management subnet.[/am4show]
Answer and Explanation
Nat Sim
Question
A network associate is configuring a router for the TUT company to provide internet access. The ISP has provided the company six public IP addresses of 198.18.184.105 198.18.184.110. The company has 14 hosts that need to access the internet simultaneously. The hosts in the company LAN have been assigned private space addresses in the range of 192.168.100.17 – 192.168.100.30.
|
The following have already been configured on the router: – The basic router configuration |
Tasks:
+ Use NAT to provide Internet access to all hosts in the company LAN.
+ Name the router TUT
+ Inside global addresses: 198.18.184.105 198.18.184.110/29
+ Inside local addresses: 192.168.100.17 – 192.168.100.30/28
+ Numer of inside hosts: 14
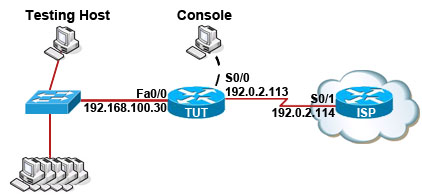
Solution:
OSPF Sim
Question
9tut.net company has decided to network three locations to improve efficiency in inventory control. The routers have been named to reflect the location: Boston, Frankfurt, Lancaster.
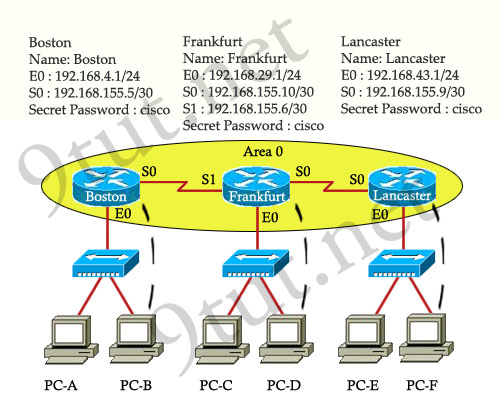
The necessary networking has been completed at each location, and the routers have been configured with single area OSPF as the routing protocol. The Boston router was recently installed but connectivity is not complete because of incomplete routing tables. Identify and correct any problem you see in the configuration.
Note: The OSPF process must be configured to allow interfaces in specific subnets to participate in the routing process.
You can download this lab and open with Packet Tracer here: https://www.9tut.net/download/OSPF_Sim_with_Solution.zip. Please say thanks to Renan who shared the files with us!
Answer and Explanation:
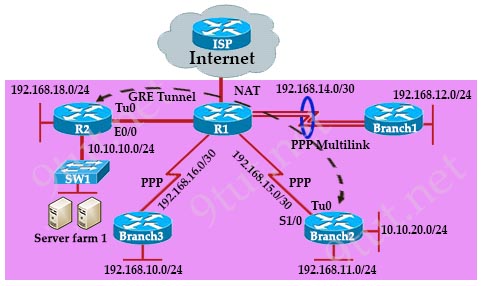
GRE Multilink Sim
[am4show have=’p2;’]
Premium Member: You can practice this sim with our simulator here.[/am4show]
Refer to the topology below and answer the following questions.
STP Questions
Here you will find answers to STP Questions
If you are not sure about STP, please read my Spanning Tree Protocol tutorial first.
Question 1
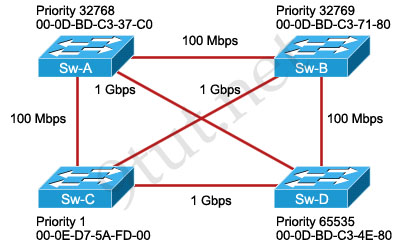
Which switch will be chosen as root bridge and why?
A. Sw-B, because it has the highest MAC address
B. Sw-A, because it has the lowest MAC address
C. Sw-C, because it has the lowest priority
D. Sw-D, because it has the highest priority
Answer: C
Explanation
The bridge with the lowest bridge ID will become the root bridge. The bridge ID = Priority + MAC so the lowest priority will be chosen first. If all switches’ priorities all equal then their MAC will be compared (the lowest is the best).
Question 2
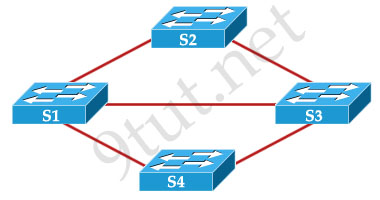
Spanning Tree Protocol has created a loop-free logical topology in the network that is pictured. How many ports have been placed in the blocking mode?
A. two
B. none
C. three
D. one
E. four
Answer: A
Explanation
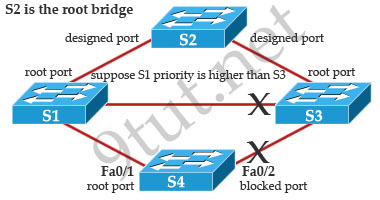
The best way to solve this question is to suppose that one of these switches is the root switch (bridge). For example, if we choose S2 the root bridge and all of its ports will be in forwarding state (so that they are not blocked).
Also suppose that S1 has higher priority than S3 -> the port on S3 connected to S1 will be blocked.
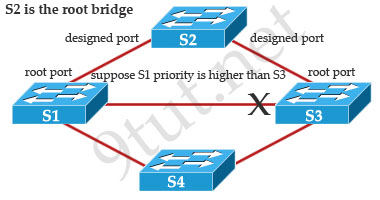
The most difficult problem is that how can we know which port on S4 will be in blocking state. Well, it depends on the Sending Port ID on S4 (Port ID = port priority + port index). If using default values, the default port priority’s value is the same, so S4 will compare port index values, which are unique to each port on the switch. One more time, we suppose S4 connects to S1 via Fa0/1 and S4 connects to S3 via Fa0/2. Because Fa0/2 is inferior to Fa0/1, S4 will select the port connected with Fa0/1 as its root port and block the other port.
Question 3
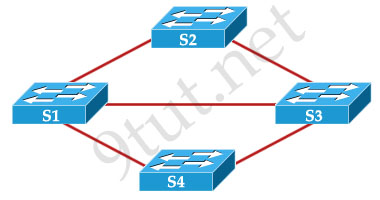
What is the way that Spanning Tree Protocol prevents switching loops based on the exhibit provided?
A. STP shuts down S3 to eliminate the switching loops.
B. STP identifies cables that must be disconnected to eliminate the redundant paths.
C. STP load balances traffic evenly across the redundant links.
D. STP places ports into the blocking state to disable the redundant paths.
E. STP allows the switches to communicate with a router that makes the traffic forwarding decisions.
Answer: D
Question 4
The following network was designed to provide reliability through redundancy.

Both of the IDF switches, S3 and S4, are in connection with both of the MDF switches, S1 and S2. A loop-free switching environment is nedded, which configuration scenario will achieve this?
A. Spanning Tree Protocol should be running on all switches.
B. Spanning Tree Protocol should be running only on the root bridge.
C. Spanning Tree Protocol is not needed in this network.
D. Spanning Tree Protocol should be running on only the MDF switches S1 and S2.
Answer: A
Question 5
Which two values are used by Spanning Tree Protocol to elect a root bridge? (Choose two)
A. Amount of RAM
B. Bridge priority
C. IOS version
D. IP address
E. MAC address
F. Speed of the links
Answer: B E
Question 6
Which two of these statements regarding RSTP are correct? (Choose two)
A. RSTP cannot operate with PVST+.
B. RSTP defines new port roles.
C. RSTP defines no new port states.
D. RSTP is a proprietary implementation of IEEE 802.1 D STP.
E. RSTP is compatible with the original IEEE 802.1 D STP.
Answer: B E
Question 7
Which switch would STP choose to become the root bridge in the selection process?
A. 32768: 11-22-33-44-55-66
B. 32768: 22-33-44-55-66-77
C. 32769:11-22-33-44-55-65
D. 32769: 22-33-44-55-66-78
Answer: A
VTP & VLAN Questions
Here you will find answers to VTP & VLAN Questions
If you are not sure about VTP, please read my VTP tutorial and VLAN tutorial
Question 1
A network administrator is explaining VTP configuration to a new technician.
What should the network administrator tell the new technician about VTP configuration? (Choose three)
A. A switch in the VTP client mode cannot update its local VLAN database.
B. A trunk link must be configured between the switches to forward VTP updates.
C. A switch in the VTP server mode can update a switch in the VTP transparent mode.
D. A switch in the VTP transparent mode will forward updates that it receives to other switches.
E. A switch in the VTP server mode only updates switches in the VTP client mode that have a higher VTP revision number.
F. A switch in the VTP server mode will update switches in the VTP client mode regardless of the configured VTP domain membership.
Answer: A B D
Question 2
ALSwitch1# show running-config
«output omitted»
interface FastEthernet0/24 no ip address
«output omitted»
ALSwitch1# show interfaces FastEthernet0/24 switchport
Name: Fa0/24
Switchport: Enable
Administrative Mode: static access
Operation Mode: static access
Administrative Trunking Encapsulation: dot1q
Operation Trunking Encapsulation: native
Negotiation of Trunking: Off
Access Mode VLAN: 1 (default)
Trunking Native Mode VLAN: 1 (default)
Voice VLAN: none
Administrative private-vlan host-association: none
Administrative private-vlan mapping: none
Operation private-vlan: none
Trunking VLANs Enabled: ALL
Pruning VLANs Enabled: 2-1001
Capture Mode Disabled
Capture VLANs Allowed: ALL
Protected: false
Voice VLAN: none (Inactive)
Aplliance trust: none
Switch port FastEthernet 0/24 on ALSwitch1 will be used to create an IEEE 802.1 Q-compliant trunk to another switch.
What is the reason the trunk does not form, even though the proper cabling has been attached?
A. VLANs have not been created yet.
B. An IP address must be configured for the port.
C. The port is currently configured for access mode.
D. The correct encapsulation type has not been configured.
E. The no shutdown command has not been entered for the port.
Answer: C
Question 3
Which statements describe two of the benefits of VLAN Trunking Protocol? (Choose two)
A. VTP allows routing between VLANs.
B. VTP allows a single switch port to carry information to more than one VLAN.
C. VTP allows physically redundant links while preventing switching loops.
D. VTP simplifies switch administration by allowing switches to automatically share VLAN configuration information.
E. VTP helps to limit configuration errors by keeping VLAN naming consistent across the VTP domain.
F. VTP enhances security by preventing unauthorized hosts from connecting to the VTP domain.
Answer: D E
Explanation
VLAN Trunking Protocol (VTP) is used to ensure that all switches in a given group, or VTP domain, have the same information about the VLANs that are present in that domain. When VTP is turned on, switches will automatically share its VLANs information to other switches (which are in the same domain) by VTP updates.
Question 4
Which two link protocols are used to carry multiple VLANs over a single link? (Choose two)
A. VTP
B. 802.1q
C. IGP
D. ISL
E. 802.3u
Answer: B D
Explanation
The Inter-Switch Link (ISL) and 802.1Q protocols are used to establish trunk links carrying traffic for multiple VLANs.
Question 5
Which three of these statements regarding 802.1Q trunking are correct? (Choose three)
A. 802.1Q native VLAN frames are untagged by default.
B. 802.1Q trunking ports can also be secure ports.
C. 802.1Q trunks can use 10 Mb/s Ethernet interfaces.
D. 802.1Q trunks require full-duplex, point-to-point connectivity.
E. 802.1Q trunks should have native VLANs that are the same at both ends.
Answer: A C E
Explanation
Native VLAN frames are carried over the trunk link untagged -> A is correct.
802.1Q trunking ports carry all the traffic of all VLANs so it cannot be the secure ports. A secure port should be only configured to connect with terminal devices (hosts, printers, servers…) -> B is not correct.
The Inter-Switch Link (ISL) encapsulation requires FastEthernet or greater to operate but 802.1q supports 10Mb/s Ethernet interfaces. -> C is correct.
802.1Q supports point-to-multipoint connectivity. Although in Cisco implementation, a “trunk” is considered a point-to-point link but 802.1q encapsulation can be used on an Ethernet segment shared by more than two devices. Such a configuration is seldom needed but is still possible with the disablement of DTP negotiation. -> D is not correct (Reference: http://www.cisco.com/en/US/products/hw/switches/ps700/products_tech_note09186a008012ecf3.shtml)
The native VLAN that is configured on each end of an 802.1Q trunk must be the same. This is because when a switch receives an untagged frame, it will assign that frame to the native VLAN. If one end is configured VLAN1 as the native VLAN while the other end is configured VLAN2 as the native VLAN, a frame sent in VLAN1 on one side will be received on VLAN2 on the other side -> E is correct.
RIP Questions
Here you will find answers to RIP Questions
Note: If you are not sure about RIP, please read my RIP tutorial
Question 1
What are two characteristics of RIPv2? (Choose two)
A.classful routing protocol
B. variable-length subnet masks
C. broadcast addressing
D. manual route summarization
E. uses SPF algorithm to compute path
Answer: B D
Question 2
Router_1# show ip protocols
Routing Protocol is “rip”
Sending updates every 30 seconds, next due in 8 seconds
Invalid after 180 seconds, hold down 180, flushed after 240
Outgoing update filter list for all interfaces is not set
Incoming update filter list for all interfaces is not set
After a RIP route is marked invalid on Router_1, how much time will elapse before that route is removed from the routing table?
A. 30 seconds
B. 60 seconds
C. 90 seconds
D. 180 seconds
E. 240 seconds
Answer: B
Explanation
The invalid and flush timers start at the same time and run concurrently. So after a RIP route is marked invalid, it will take 240 – 180 = 60 seconds for that route to be removed from the routing table.
Question 3
Which three statements are correct about RIP version 2? (Choose three)
A. It has the same maximum hop count as version 1.
B. It uses broadcasts for its routing updates.
C. It is a classless routing protocol.
D. It has a lower default administrative distance than RIP version 1.
E. It supports authentication.
F. It does not send the subnet mask in updates.
Answer: A C E
Question 4

HQ(config)# router rip
HQ(config-router)# network 172.16.0.0
HQ(config-router)# exit
HQ(con£ig)# ip route 172.16.15.0 255.255.255.0 172.16.18.2 150
Assuming that the routing protocol for the entire network is RIP, and the RIP is configured with its default settings. You properly configure all links and all these links are functioning normally.
Regarding the network described which of the following statements are true? (Choose two)
A. The HQ router will prefer to use its S0 interface to reach E1 of the Branch router.
B. The HQ will prefer to use its BRIO interface to reach E1 on the Branch router.
C. The HQ BRI0 interface will be used to reach the Branch E1 network in the event the S0 link fails.
D. The HQ S0 interface will be used to reach the Branch E1 network in the event the BRI0 link fails.
Answer: A C
Explanation
The HQ router is configured with both static and RIP to reach 172.16.15.0/24 network so it has to use the Administrative Distance of each route to decide which route should it forward the packet to. The static route “ip route 172.16.15.0 255.255.255.0 172.16.18.2 150” is configured with an AD of 150 but the default AD of RIP route is 120 so the RIP path will be favored over static route.
Question 5
Which statement about RIPng is true?
A. RIPng allows for routes with up to 30 hops.
B. RIPng is enabled on each interface separately.
C. RIPng uses broadcasts to exchange routes.
D. There can be only one RIPng process per router.
Answer: B
Explanation
The Routing Information Protocol next generation (RIPng) is an interior gateway protocol (IGP) that uses a distance-vector algorithm to determine the best route to a destination, using the hop count as the metric. RIPng is a routing protocol that exchanges routing information used to compute routes and is intended for Internet Protocol version 6 (IPv6)-based networks.
RIPng is enabled on each interface separately. Below is an example:
R1(config)#ipv6 router rip 9tut //name the process RIPng 9tut
R1(config-rtr)#exit
R1(config)#interface E0/0
R1(config-if)#ipv6 rip 9tut enable //run RIPng 9tut process on E0/0
Question 6
A medium-sized company has a Class C IP address. It has two Cisco routers and one non-Cisco router.
All three routers are using RIP version 1.
The company network is using the block of 198.133.219.0/24.
The company has decided it would be a good idea to split the network into three smaller subnets and create the option of conserving addresses with VLSM.
What is the best course of action if the company wants to have 40 hosts in each of the three subnets?
A. Convert all the routers to EIGRP and use 198.133.219.32/27,198.133.219.64/27, and 198.133.219.92/27 as the new subnetworks.
B. Maintain the use of RIP version 1 and use 198.133.219.32/27,198.133.219.64/27, and 198.133.219.92/27 as the new subnetworks.
C. Convert all the routers to EIGRP and use 198.133.219.64/26,198.133.219.128/26, and 198.133.219.192/26 as the new subnetworks.
D. Convert all the routers to RIP version 2 and use 198.133.219.64/26,198.133.219.128/26, and 198.133.219.192/26 as the new subnetworks.
E. Convert all the routers to OSPF and use 198.133.219.16/28,198.133.219.32/28, and 198.133.219.48/28 as the new subnetworks.
F. Convert all the routers to static routes and use 198.133.219.16/28,198.133.219.32/28, and 198.133.219.48/28 as the new subnetworks.
Answer: D
Question 7

The network shown in the exhibit is running the RIPv2 routing protocol. The network has converged, and the routers in this network are functioning properly.
The FastEthernet0/0 interface on R1 goes down. In which two ways will the routers in this network respond to this change? (Choose two)
A. All routers will reference their topology database to determine if any backup routes to the 192.168.1.0 network are known.
B. Routers R2 and R3 mark the route as inaccessible and will not accept any further routing updates from R1 until their hold-down timers expire.
C. Because of the split-horizon rule, router R2 will be prevented from sending erroneous information to R1 about connectivity to the 192 168.1.0 network.
D. When router R2 learns from R1 that the link to the 192.168.1.0 network has been lost, R2 will respond by sending a route back to R1 with an infinite metric to the 192.168.1.0 network.
E. R1 will send LSAs to R2 and R3 informing them of this change, and then all routers will send periodic updates at an increased rate until the network again converges.
Answer: C D
Question 8
What is the default routing update period for RIPv2?
A. 15 seconds
B. 30 Seconds
C. 180 Seconds
D. 240 Seconds
Answer: B
Question 9
What two things will a router do when running a distance vector routing protocol? (Choose two)
A. Send periodic updates regardless of topology changes.
B. Send entire routing table to all routers in the routing domain.
C. Use the shortest-path algorithm to the determine best path.
D. Update the routing table based on updates from their neighbors.
E. Maintain the topology of the entire network in its database.
Answer: A D
EIGRP Questions
Here you will find answers to EIGRP Questions
Note: If you are not sure about EIGRP, please read my EIGRP tutorial
Question 1
A router has learned three possible routes that could be used to reach a destination network.
One route is from EIGRP and has a composite metric of 20514560. Another route is from OSPF with a metric of 782. The last is from RIPv2 and has a metric of 4.
Which route or routes will the router install in the routing table?
A. the OSPF route
B. the EIGRP route
C. the RIPv2 route
D. all three routes
E. the OSPF and RIPv2 routes
Answer: B
Explanation
Regardless of the metric value, EIGRP has the lowest Administrative Distance (AD) so it will be used and routes learned from EIGRP will be installed in the routing table. Some popular ADs are listed below:
+ Static route: 1
+ RIPv1 & RIPv2: 120
+ IGRP & EIGRP: 90
+ OSPF: 110
Question 2
HQ_Router# show ip protocols
Routing Protocol is “eigrp 109”
Outgoing update filter list for all interfaces is not set
Incoming update filter list for all interfaces is not set
Default networks flagged in outgoing updates
Default networks accepted from incoming updates
EIGRP metric weight K1=1, K2=0, K3=1, K4=0, K5=0
EIGRP maximum hopcount 100
EIGRP maximum metric variance 1
Redistributing: eigrp 109
Automatic network summarization is in effect
Automatic address summarization: 20.0.0.0/0 for FastEthernet0/1
Summarizing with metric 28160 172.30.0.0/16 for FastEthernet0/0
Summarizing with metric 28160
Maximum path: 4
Routing for Networks:
20.0.0.0
172.30.0.0
192.160.1.0
Routing Information Sources:
Gateway Distance Last Update
20.10.10.2 90 260796
172.30.10.2 90 454765
Distance: internal 90 external 170
How many paths can the EIGRP routing process use to forward packets from HQ_Router to a neighbor router?
A. two equal-cost paths
B. two unequal-cost paths
C. three equal-cost paths
D. three unequal-cost paths
E. four equal-cost paths
F. four unequal-cost paths
Answer: E
Explanation
Because the “EIGRP maximum metric variance” is 1 so only equal-cost paths are used.
The “Maximum path” is 4 so EIGRP can use up to 4 paths to forward packets.
Therefore EIGRP can only use four equal-cost paths -> E is correct.
Notice: This question has another version with “EIGRP maximum metric variance” is set to a value greater than 1 than the answer should be “four unequal-cost paths” can be used.
Question 3
Fabrikant Incorporated is a worldwide finance provider. The network uses EIGRP as its routing protocol throughout the corporation. The network administrator does not understand the convergence of EIGRP. Using the output of the show ip eigrp topology all-links command, answer the administrators questions:
Switch1# show ip eigrp topology all-links
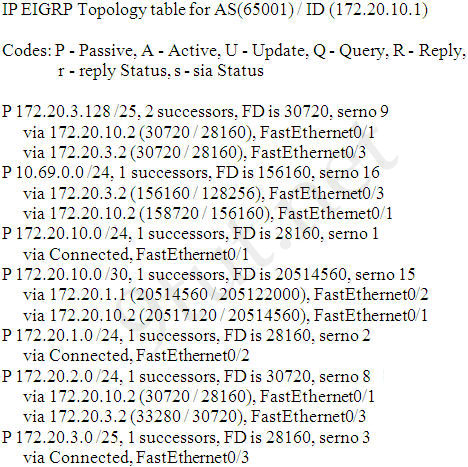
Which three EIGRP routes will be installed for the 172.20.3.128 /25 and 172.20.2.0/24 networks? (choose three)
A. 172.20.3.128 /25 [90/28160] via 172.20.1.2 01:26:35. FastEthernet0/2
B. 172.20.3.128 /25 [90/30720] via 172.20.3.2 01:26:35. FastEthernet0/3
C. 172.20.3.128 /25 [90/30720] via 172.20.10.2 01:26:35. FastEthernet0/1
D. 172.20.2.0 /24 [90/30720] via 172.20.10.2 02:10:11. FastEthernet0/1
E. 172.20.2.0 /24 [90/28160] via 172.20.10.2 02:10:11. FastEthernet0/1
F. 172.20.2.0 /24 [90/33280] via 172.20.3.2 02:10:11. FastEthernet0/1
Answer: B C D
Explanation
There is a similar question posted at http://www.digitaltut.com/route-eigrp-simlet. Please read the explanation there and try to answer this question.
Question 4 (same question as question 3)
Switch1# show ip eigrp topology all-links
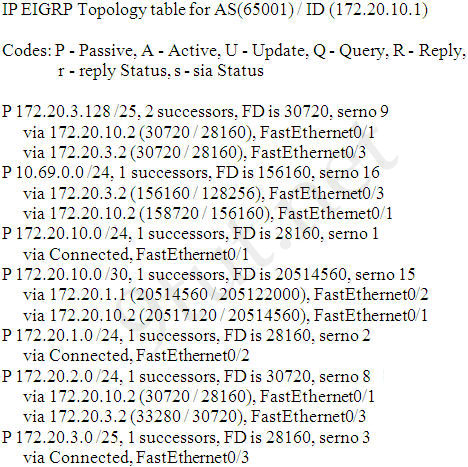
Which three networks does the Switch1 device have feasible successors for? (Choose three)
A. 172.20.10.0 /30
B. 172.20.1.0 /24
C. 172.20.2.0 /24
D. 172.20.3.0 /25
E. 172.20.3.128/25
F. 10.69.0.0/24
Answer: A C F
Question 5
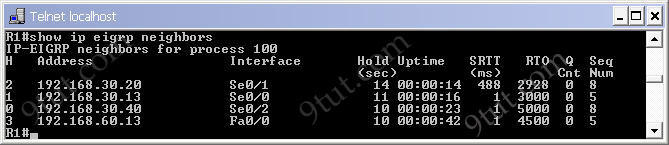
A network administrator is troubleshooting an EIGRP problem on a router and needs to confirm the IP addresses of the devices with which the router has established adjacency. The retransmit interval and the queue counts for the adjacent routers also need to be checked.
What command will display the required information?
A. Router# show ip eigrp topology
B. Router# show ip eigrp interfaces
C. Router# show ip eigrp adjacency
D. Router# show ip eigrp neighbors
Answer: D
Explanation
Below is an example of the “show ip eigrp neighbors” command (from 9tut.com)
Question 6
As a Cisco technician, you need to know EIGRP protocol very well. Which of the following is true about EIGRP successor routes? (Choose two)
A. A successor route is used by EIGRP to forward traffic to a destination.
B. Successor routes are saved in the topology table to be used if the primary route fails.
C. Successor routes are flagged as “active” in the routing table.
D. A successor route may be backed up by a feasible successor route.
E. Successor routes are stored in the neighbor table following the discovery process.
Answer: A D
Question 7
Problems may occur when a routing protocol tries to identify the next hop in discontinuous networks in the IP addressing scheme. But some routing protocols may minimize the effects of the problems.
Which are these routing protocols? (Choose three)
A. EIGRP
B. VLSM
C. OSPF
D. RIP v2
Answer: A C D
Explanation
Classless routing protocols can be used in discontinuous networks as they do send the subnet mask in their updates so Variable Length Subnet Masks (VLSMs) are supported.
Question 8
Glencoe#show ip protocol
Routing Protocol is “eigrp 478”
— output omitted —
Redistributing: eigrp 478
Automatic network summarization is not in effect
Maximum path: 4
Routing for Networks:
172.26.168.128/26
172.26.169.0/26
Routing Information Sources:
Gateway Distance Last Update
172.26.168.129 90 01:01:59
Distance: internal 90 external 170
The EIGRP configuration in the Glencoe router uses a single network statement.
From the output shown in the graphic, which network statement would advertise these networks in EIGRP?
A. network 172.26.168.128 area 478
B. network 172.26.0.0
C. network 172.26.168.0 area 478
D. network 172.26.168.128 0.0.0.127
Answer: B
Question 9
What will a router do if it does not have EIGRP feasible successor route to a destination network and the successor route to that destination network is in active status?
A. It broadcasts Hello packets to all routers in the network to re-establish neighbor adjacencies.
B. It routes all traffic that is addressed to the destination network to the interface indicated in the routing table.
C. It sends a multicast query packet to all adjacent neighbors requesting available routing paths to the destination network.
D. It sends a copy of its neighbor table to all adjacent routers.
Answer: C
Question 10
The company uses EIGRP as the routing protocol.
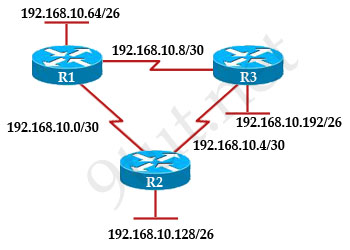
R3# show ip route
Gateway of last resort is not set
192 168.10.0/24 is variably subnetted, 6 subnets, 2 masks
D 192.168. 10.64/26 [90/2195456] via 192.168.10.9, 00:03:31, Serial0/0
D 192.168.10.0/30 [90/2681856] via 192.168.10.9, 00:03:31, Serial0/0
C 192.168.10.4/30 is directly connected, Serial 0/1
C 192.168.10.8/30 is directly connected, Serial 0/0
C 192.168.10.192/26 is directly connected, FastEthernet0/0
D 192.168.10.128/26 [90/2195456] via 192.168.10.5,00:03 31, Serial 0/1
What path will packets take from a host on 192.168.10.192/26 network to a host on the LAN attached to router R1?
A. The path of the packets will be R3 to R2 to R1.
B. The path of the packets will be R3 to R1 to R2.
C. The path of the packets will be both R3 to R2 to R1 and R3 to R1.
D. The path of the packets will be R3 to R1.
Answer: D
Explanation
From the line “D 192.168. 10.64/26 [90/2195456] via 192.168.10.9, 00:03:31, Serial0/0″ we can see the IP address 192.168.10.9 belongs to network 192.168.10.8/30 and this network is between R1 and R3 -> Packet from 192.168.10.192/26 network destined to a host on the LAN attached to router R1 will go directly from R3 to R1.
EIGRP Questions 2
Here you will find answers to EIGRP Questions – Part 2
Note: If you are not sure about EIGRP, please read my EIGRP tutorial
Question 1
Which two statements are true regarding EIGRP? (Choose two)
A. Passive routes are in the process of being calculated by DUAL
B. EIGRP supports VLSM, route summarization, and routing update authentication.
C. EIGRP exchanges full routing table information with neighboring routers with every update.
D. If the feasible successor has a higher advertised distance than the successor route, it becomes the primary route.
E. A query process is used to discover a replacement for a failed route if a feasible successor is not identified from the current routing information.
Answer: B E
Question 2
The following are four types of EIGRP route entries. Which of them describes a feasible successor?
A. a backup route, stored in the routing table
B. a primary route, stored in the topology table
C. a primary route, stored in the routing table
D. a backup route, stored in the topology table
Answer: D
Explanation
EIGRP builds and maintains three tables:
+ Neighbor table: lists directly connected routers running EIGRP with which this router has an adjacency
+ Topology table: lists all routes learned from each EIGRP neighbor -> the feasible successors are stored here!
+ Routing table: lists all best routes from the EIGRP topology table and other routing processes -> only successors are stored here.
Question 3
Below is the output of a router.
Gateway of last resort is not set
192.168.25.0 /30 is subnetted, 4 subnets
D 192.168.25.20 [90/2681856] via 192.168.15.5, 00:00:10, Serial0/1
D 192.168.25.16 [90/1823638] via 192.168.15.5, 00:00:50, Serial0/1
D 192.168.25.24 [90/3837233] via 192.168.15.5, 00:05:23, Serial0/1
D 192.168.25.28 [90/8127323] via 192.168.15.5, 00:06:45, Serial0/1
C 192.168.15.4/30 is directly connected, Serial0/1
C 192.168.2.0/24 is directly connected, FastEthernet0/0
Which address and mask combination represents a summary of the routes learned by EIGRP?
A. 192.168.25.0 255.255.255.240
B. 192.168.25.28 255.255.255.240
C. 192.168.25.16 255.255.255.252
D. 192.168.25.16 255.255.255.240
E. 192.168.25.28 255.255.255.252
F. 192.168.25.0 255.255.255.252
Answer: D
Explanation
From the output above, EIGRP learned 4 routes and we need to find out the summary of them:
+ 192.168.25.16
+ 192.168.25.20
+ 192.168.25.24
+ 192.168.25.28
-> The increment should be: 28 – 16 = 12 but 12 is not an exponentiation of 2 so we must choose 16 (24). Therefore the subnet mask is /28 (=1111 1111.1111 1111.1111 1111.1111 0000) = 255.255.255.240
So the best answer should be 192.168.25.16 255.255.255.240
Question 4
Enhanced Interior Gateway Routing Protocol – (EIGRP) is a Cisco proprietary routing protocol loosely based on their original IGRP. A router has EIGRP configured as the only routing protocol.
How does EIGRP respond if there is no feasible successor route to a destination network and the successor route fails?
A. It immediately sends its entire routing table to its neighbors.
B. EIGRP sends a Hello packet to the DR to inform it of the route failure.
C. It automatically forwards traffic to a fallback default route until a new successor route is found.
D. It sends queries out to neighbors until a new successor route is found.
E. It places the route in holddown until LSA updates inform it of a new route to the network.
Answer: D
Explanation
EIGRP sends a query when a route is lost and the feasible route (for that path) does not exist in the topology table
Question 5
Router# show ip eigrp topology 10.0.0.5 255.255.255.255
IP-EIGRP topology entry for 10.0.0.5/32 State is Passive, Query origin flag is 1, 1 Successor(s), FD is 41152000
Given the output from the show ip eigrp topology command, which router is the feasible successor?
A. Router A.
10.1.0.1 (serial0), from 10.1.0.1 composite
metric is 46152000/41640000
B. Router B.
10.0.0.2 (serial0.1), from 10.0.0.2
composite metric is 53973240/120256
C. Router C.
10.1.0.3 (serial0), from 10.1.0.3
composite metric is 46866176/46354176
D. Router D.
10.1.1.1 (serial0.1), from 10.1.1.1
composite metric is 46670776/46251776
Answer: B
Explanation
First we must notice that all the 4 answers are parts of the “show ip eigrp topology” output. As you can see, there are 2 parameters in the form of [FD/AD] in each answer. For example answer A has [46152000/41640000], it means that the FD of that route is 46152000 while the AD is 41640000.
To become a feasible successor, a router must meet the feasibility condition:
“To qualify as a feasible successor, a router must have an AD less than the FD of the current successor route“
In four answer above, only answer B has an AD of 120256 and it is smaller than the FD of the current successor route (41152000) so it is the feasible successor -> B is correct.
Question 6

When running EIGRP what is required for RouterA to exchange routing updates with RouterC?
A. AS numbers must be changed to match on all the routers.
B. Loopback interface must be configured so a DR is elected.
C. The no auto-summary command is needed on Router A and Router C.
D. Router B needs to have two network statements, one for each connected network.
Answer: A
Explanation
We notice that 3 routers are using different AS numbers so they do not become neighbors and cannot exchange their routing updates. We need to choose only one AS number and use it on all 3 routers to make them exchange routing updates.
In this case we don’t need to use the “no auto-summary” command because network 10.0.0.0 is not separated by another major network.
Question 7
For the following routing protocols, which one uses bandwidth and delay as metrics by default?
A. EIGRP
B. RIP
C. BGP
D. OSPF
Answer: A
Question 8
A router is running three routing processes: RIP, OSPF, and EIGRP, each configured with default characteristics. Each process learns a route to the same remote network.
If there are no static routes to the destination and none of the routes were redistributed, which route will be placed in the IP routing table?
A. the route learned through EIGRP
B. the route learned through OSPF
C. the route learned through RIP
D. the route with the lowest metric
E. all three routes with the router load balancing
Answer: A
Question 9
To support the following IP addressing scheme, which routing protocols will be used? (Choose three)
Network 1 -192.168.10.0/26
Network 2 -192.168.10.64/27
Network 3- 192.168.10.96/27
Network 4-192.168.10.128/30
Network 5-192.168.10.132 /30
A. EIGRP
B. IGRP
C. OSPF
D. RIP version 2
E. RIP version 1
F. VTP
G. CDP
Answer: A C D
Explanation
All 5 networks above are subnetted -> all the classless routing protocols can be used as they do send the subnet mask in their updates so Variable Length Subnet Masks (VLSMs) are supported.
Question 10
Which routing protocols can be used within the enterprise network shown in the diagram? (Choose three)
A. RIP v1
B. RIPv2
C. IGRP
D. OSPF
E. BGP
F. EIGRP
Answer: B D F
OSPF Questions
Here you will find answers to OSPF Questions
Note: If you are not sure about OSPF, please read my OSPF tutorial
Question 1
After the network has converged, what type of messaging, if any, occurs between R3 and R4?
A. No messages are exchanged.
B. Hellos are sent every 10 seconds.
C. The full database from each router is sent every 30 seconds.
D. The routing table from each router is sent every 60 seconds.
Answer: B
Explanation
HELLO messages are used to maintain adjacent neighbors so even when the network is converged, hellos are still exchanged. On broadcast and point-to-point links, the default is 10 seconds, on NBMA the default is 30 seconds.
Although OSPF is a link-state protocol but the full database from each router is sent every 30 minutes (not seconds) -> C and D are not correct.
Question 2
R1 is configured with the default configuration of OSPF.
From the following list of IP addresses configured on R1, which address will the OSPF process select as the router ID?
A. 192.168.0.1
B. 172.16.1.1
C. 172.16.2.1
D. 172.16.2.225
Answer: A
Explanation
The Router ID (RID) is an IP address used to identify the router and is chosen using the following sequence:
+ The highest IP address assigned to a loopback (logical) interface.
+ If a loopback interface is not defined, the highest IP address of all active router’s physical interfaces will be chosen.
+ The router ID can be manually assigned
In this case, because a loopback interface is not configured so the highest active IP address 192.168.0.1 is chosen as the router ID.
Question 3
What information does a router running a link-state protocol use to build and maintain its topological database? (Choose two)
A. hello packets
B. SAP messages sent by other routers
C. LSAs from other routers
D. beacons received on point-to-point links
E. routing tables received from other link-state routers
F. TTL packets from designated routers
Answer: A C
Question 4
R1 is unable to establish an OSPF neighbor relationship with R3. What are possible reasons for this problem? (Choose two)
A. All of the routers need to be configured for backbone Area 1.
B. R1 and R2 are the DR and BDR, so OSPF will not establish neighbor adjacency with R3.
C. A static route has been configured from R1 to R3 and prevents the neighbor adjacency from being established.
D. The hello and dead interval timers are not set to the same values on R1 and R3.
E. EIGRP is also configured on these routers with a lower administrative distance.
F. R1 and R3 are configured in different areas.
Answer: D F
Explanation
To become OSPF neighbors, routers must meet these requirements: Hello interval, Dead interval and AREA number -> D and F are correct.
Question 5
ROUTER# show ip route
192.168.12.0/24 is variably subnetted, 9 subnets, 3 masks
C 192.168.12.64 /28 is directly connected, Loopback1
C 192.168.12.32 /28 is directly connected, Ethernet0
C 192.168.12.48 /28 is directly connected, Loopback0
O 192.168.12.236 /30 [110/128] via 192.168.12.233, 00:35:36, Serial0
C 192.168.12.232 /30 is directly connected, Serial0
O 192.168.12.245 /30 [110/782] via 192.168.12.233, 00:35:36, Serial0
O 192.168.12.240 /30 [110/128] via 192.168.12.233, 00:35:36, Serial0
O 192.168.12.253 /30 [110/782] via 192.168.12.233, 00:35:37, Serial0
O 192.168.12.249 /30 [110/782] via 192.168.12.233, 00:35:37, Serial0
O 192.168.12.240/30 [110/128] via 192.168.12.233, 00:35:36, Serial 0
To what does the 128 refer to in the router output above?
A. OSPF cost
B. OSPF priority
C. OSPF hop count
D. OSPF ID number
E. OSPF administrative distance
Answer: A
Explanation
The first parameter is the Administrative Distance of OSPF (110) while the second parameter is the cost of OSPF.
Question 6
Which of the following describe the process identifier that is used to run OSPF on a router? (Choose two)
A. It is locally significant.
B. It is globally significant.
C. It is needed to identify a unique instance of an OSPF database.
D. It is an optional parameter required only if multiple OSPF processes are running on the router.
E. All routers in the same OSPF area must have the same process ID if they are to exchange routing information.
Answer: A C
Question 7
Open Shortest Path First (OSPF) is a routing protocol developed for Internet Protocol (IP) networks by the Interior Gateway Protocol (IGP) working group of the Internet Engineering Task Force (IETF). What is the default administrative distance of the OSPF routing protocol?
A. 90
B. 100
C. 110
D. 20
E. 130
F. 170
Answer: C
Question 8
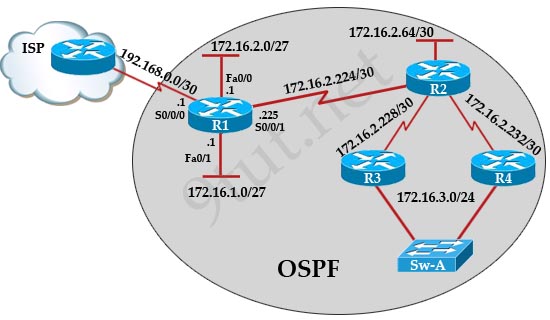
The internetwork infrastructure of company XYZ consists of a single OSPF area as shown in the graphic.
There is concern that a lack of router resources is impeding internetwork performance.
As part of examining the router resources the OSPF DRs need to be known.
All the router OSPF priorities are at the default and the router IDs are shown with each router.
Which routers are likely to have been elected as DR? (Choose two)
A. Corp-1
B. Corp-2
C. Corp-3
D. Corp4
E. Branch-1
F. Branch-2
Answer: D F
Explanation
There are 2 segments on the topology above which are separated by Corp-3 router. Each segment will have a DR so we have 2 DRs.
To select which router will become DR they will compare their router-IDs. The router with highest (best) router-ID will become DR. The router-ID is chosen in the order below:
+ The highest IP address assigned to a loopback (logical) interface.
+ If a loopback interface is not defined, the highest IP address of all active router’s physical interfaces will be chosen.
In this question, the IP addresses of loopback interfaces are not mentioned so we will consider IP addresses of all active router’s physical interfaces. Router Corp-4 (10.1.40.40) & Branch-2 (10.2.20.20) have highest “active” IP addresses so they will become DRs.
Question 9
Which address are OSPF hello packets addressed to on point-to-point networks?
A. 224.0.0.5
B. 172.16.0.1
C. 192.168.0.5
D. 223.0.0.1
E. 254.255.255.255
Answer: A
Question 10
Which statements describe the routing protocol OSPF? (Choose three)
A. It supports VLSM.
B. It is used to route between autonomous systems.
C. It confines network instability to one area of the network.
D. It increases routing overhead on the network.
E. It allows extensive control of routing updates.
F. It is simpler to configure than RIP v2.
Answer: A C E
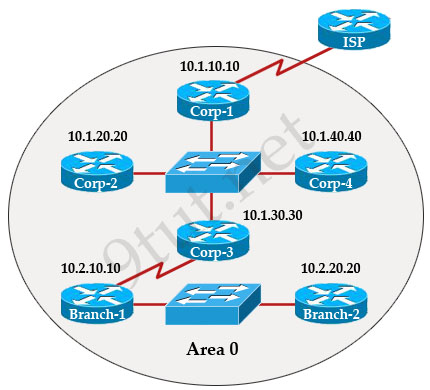
Question 11
R1 is unable to establish an OSPF neighbor relationship with R3
What are possible reasons for this problem? (Choose two)
A. All of the routers need to be configured for backbone Area 1
B. R1 and R2 are the DR and BDR, so OSPF will not establish neighbor adjacency with R3
C. A static route has been configured from R1 to R3 and prevents the neighbor adjacency from being established.
D. The hello and dead interval timers are not set to the same values on R1 and R3
E. EIGRP is also configured on these routers with a lower administrative distance
F. R1 and R3 are configured in different areas
Answer: D F
Question 12
RouterD# show ip interface brief
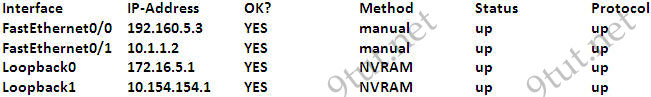
Given the output for this command, if the router ID has not been manually set, what router ID will OSPF use for this router?
A. 10.1.1.2
B. 10.154.154.1
C. 172.16.5.1
D. 192.168.5.3
Answer: C
OSPF Questions 2
Here you will find answers to OSPF Questions – Part 2
Note: If you are not sure about OSPF, please read my OSPF tutorial
Question 1
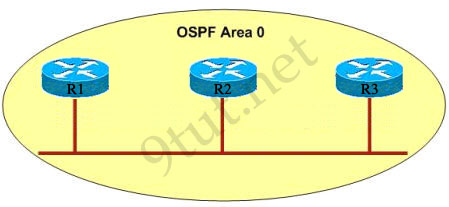
OSPF routing uses the concept of areas. What are the characteristics of OSPF areas? (Choose three)
A. Each OSPF area requires a loopback interface to be configured.
B. Areas may be assigned any number from 0 to 65535.
C. Area 0 is called the backbone area.
D. Hierarchical OSPF networks do not require multiple areas.
E. Multiple OSPF areas must connect to area 0.
F. Single area OSPF networks must be configured in area 1.
Answer: C D E
Explanation
C and E are correct according to the theory of OSPF. For answer E, it is a bit unclear but we can understand “Hierarchical OSPF networks do not require multiple areas” is correct because there are networks that are small enough to use only area 0 for the whole network.
Question 2
Open Shortest Path First (OSPF) is a dynamic routing protocol for use in Internet Protocol (IP) networks.
If configuring all OSPF routers in a single area with the same priority value, what value does a router use for the OSPF router ID in the absence of a loopback interface?
A. the IP address of the first Fast Ethernet interface
B. the IP address of the console management interface
C. the highest IP address among its active interfaces
D. the lowest IP address among its active interfaces
E. the priority value until a loopback interface is configured
Answer: C
Question 3
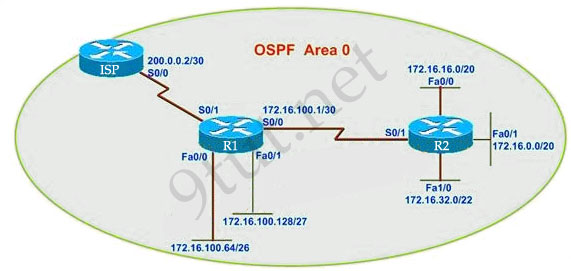
R1 routing commands:
ip route 0.0.0.0 0.0.0.0 serial0/0
router ospf 1
network 172.16.100.0 0.0.0.3 area 0
network 172.16.100.64 0.0.0.63 area 0
network 172.16.100.128 0.0.0.31 area 0
default-information originate
Assuming that all router interfaces are operational and correctly configured, that OSPF has been correctly configured on router R2, how will the default route configured on R1 affect the operation of R2?
A. Any packet destined for a network that is not directly connected to router R1 will be dropped.
B. Any packet destined for a network that is not referenced in the routing table of router R2 will be directed to R1. R1 will then send that packet back to R2 and a routing loop will occur.
C. Any packet destined for a network that is not directly connected to router R2 will be dropped immediately.
D. Any packet destined for a network that is not directly connected to router R2 will be dropped immediately because of the lack of a gateway on R1.
Answer: B
Explanation
Please read the explanation of this question at http://www.9tut.com/ccna-ospf-questions (question 6)
Question 4
Border# debug ip ospf events
OSPF events debugging is on
Border#
*Nov 4 03:49:37477: OSPF: Rev hello from 10.10.3.3 area 0 from Serial0/3 192.168.255.18
*Nov 4 03:49:37.481: OSPF: End of hello processing
*Nov 4 03:49:37.641: OSPF: Rev hello from 10.10.1.1 area 0 from Serial0/1 192.168.255.22
“Nov 4 03:49:37.645: OSPF: Mismatched hello parameters from 192.168.255.22
*Nov 4 03:49:37.645: OSPF: Dead R 40 C 56, Hello R 10 C 14
What conclusion can be drawn from the output of the debug command presented in the exhibit?
A. The output represents normal OSPF operation.
B. A router is connected to interface Serial0/3 of the Border router.
The OSPF router ID of the connected router is the IP address of the connected interface.
C. The interfaces of two OSPF routers connected to the Border router are in the same subnet.
D. The OSPF router connected to interface Serial0/1 has NOT formed a neighbor relationship with the Border router.
Answer: D
Explanation
From the debug line “Mismatched hello parameters from 192.168.255.22” we learn that there is a mismatched parameter in the hello packet (Hello interval, Dead interval or AREA number).
Question 5
Which characteristics are representative of a link-state routing protocol? (Choose three)
A. provides common view of entire topology
B. exchanges routing tables with neighbors
C. calculates shortest path
D. utilizes event-triggered updates
E. utilizes frequent periodic updates
Answer: A C D
Question 6
When running OSPF, what would cause router A not to form an adjacency with router B?
A. The loopback addresses are on different subnets.
B. The values of the dead timers on the routers are different.
C. Route summarization is enabled on both routers.
D. The process identifier on router A is different than the process identifier on router
Answer: B
Question 7
What is the OSPF router ID in a DR/BDR election used for?
A. It is used with the OSPF priority values to determine which interface will be used to form a neighbor relationship with another OSPF router.
B. It is used with the OSPF priority values to determine which OSPF router will become the DR or BDR in a point-to-point network.
C. It is used with the OSPF priority values to determine which router will become the DR or BDR in a multiaccess network.
D. It is used to determine which interfaces will send Hello packets to neighboring OSPF routers.
Answer: C
Question 8
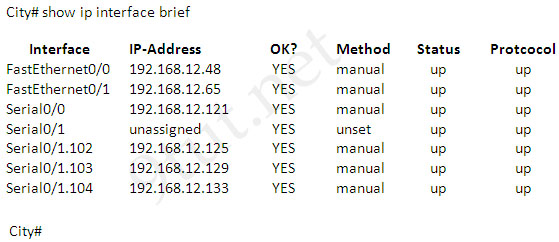
A network associate has configured OSPF with the command:
City(config-router)# network 192.168.12.64 0.0.0.63 area 0
After completing the configuration, the associate discovers that not all the interfaces are participating in OSPF.
Which three of the interfaces shown in the exhibit will participate in OSPF according to this configuration statement? (Choose three)
A. FastEthernet0/0
B. FastEthernet0/1
C. Serial0/0
D. Serial0/1.102
E. Serial0/1.103
F. Serial0/1.104
Answer: B C D
Explanation
The “network 192.168.12.64 0.0.0.63” equals to network 192.168.12.64/26. This network has:
+ Increment: 64 (/26= 1111 1111.1111 1111.1111 1111.1100 0000)
+ Network address: 192.168.12.64
+ Broadcast address: 192.168.12.127
Therefore all interface in the range of this network will join OSPF -> B C D are correct.
Question 9
To maintain connectivity with neighboring routers, routers running OSPF will send some type of packets. What is the type of packets?
A. OSP packets
B. hello packets
C. LSU packets
D. dead interval packets
Answer: B
Question 10
A network administrator is configuring the routers in the graphic for OSPF.
The OSPF process has been started and the networks have been configured for Area 0 as shown in the diagram.
The network administrator has several options for configuring RouterB to ensure that it will be preferred as the designated router (DR) for the 172.16.1.0/24 LAN segment.
What configuration tasks could be used to establish this preference? (Choose three)
A. Change the priority value of the Fa0/0 interface of RouterB to zero.
B. Configure the priority value of the Fa0/0 interface of RouterB to a higher value than any other interface on the Ethernet network.
C. Change the priority values of the Fa0/0 interfaces of RouterA and RouterC to zero.
D. Configure a loop back interface on RouterB with an IP address higher than any IP address on the other routers.
E. No further configuration is necessary.
Answer: B C D
Question 11
Open Shortest Path First (OSPF) is a dynamic routing protocol for use in Internet Protocol (IP) networks, while EIGRP is short for Enhanced Interior Gateway Routing Protocol. A large corporate which often integrates networks from newly acquired businesses has just decided to use OSPF to replace EIGRP as the corporate routing protocol.
Which two benefits will the corporation obtain by changing from EIGRP to OSPF? (Choose two)
A. the ability to automatically summarize networks
B. the ability to create a hierarchical design using areas
C. the ability to support multi-vendor routers
D. the ability to redistribute default and static routes
E. the ability to use VLSM
Answer: B C
Question 12
What are three characteristics of the OSPF routing protocol? (Choose three)
A. It converges quickly
B. OSPF is a classful routing protocol
C. It uses cost to determine the best route
D. It uses the DUAL algorithm to determine the best route
E. OSPF routers send the complete routing table to all directly attached routers
F. OSPF routers discover neighbors before exchanging routing information
Answer: A C F
Operations
Here you will find answers to ICND 2 – Operation Questions
Question 1
Refer to the exhibit. The following commands are executed on interface fa0/1 of 2950Switch.
2950Switch(config-if)#switchport port-security
2950Switch(config-if)#switchport port-security mac-address sticky
2950Switch(config-if)#switchport port-security maximum 1
The Ethernet frame that is shown arrives on interface fa0/1. What two functions will occur when this frame is received by 2950Switch? (Choose two)
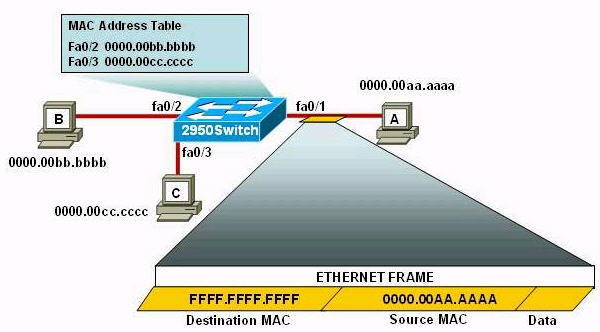
A – The MAC address table will now have an additional entry of fa0/1 FFFF.FFFF.FFFF.
B – Only host A will be allowed to transmit frames on fa0/1.
C – This frame will be discarded when it is received by 2950Switch.
D – All frames arriving on 2950Switch with a destination of 0000.00aa.aaaa will be forwarded out fa0/1.
E – Hosts B and C may forward frames out fa0/1 but frames arriving from other switches will not be forwarded out fa0/1.
F – Only frames from source 0000.00bb.bbbb, the first learned MAC address of 2950Switch, will be forwarded out fa0/1.
Answer: B D
Explanation:
The first command 2950Switch(config-if)#switchport port-security is to enable the port-security in a switch port.
In the second command 2950Switch(config-if)#switchport port-security mac-address sticky, we need to know the full syntax of this command is switchport port-security mac-address sticky [MAC]. The STICKY keyword is used to make the MAC address appear in the running configuration and you can save it for later use. If you do not specify any MAC addresses after the STICKY keyword, the switch will dynamically learn the attached MAC Address and place it into your running-configuration. In this case, the switch will dynamically learn the MAC address 0000.00aa.aaaa of host A and add this MAC address to the running configuration.
In the last command 2950Switch(config-if)#switchport port-security maximum 1 you limited the number of secure MAC addresses to one and dynamically assigned it (because no MAC address is mentioned, the switch will get the MAC address of the attached MAC address to interface fa0/1), the workstation attached to that port is assured the full bandwidth of the port.Therefore only host A will be allowed to transmit frames on fa0/1 -> B is correct.
After you have set the maximum number of secure MAC addresses for interface fa0/1, the secure addresses are included in the “Secure MAC Address” table (this table is similar to the Mac Address Table but you can only view it with the show port-security address command). So in this question, although you don’t see the MAC address of host A listed in the MAC Address Table but frames with a destination of 0000.00aa.aaaa will be forwarded out of fa0/1 interface -> D is correct.
Question 2
A network administrator must configure 200 switch ports to accept traffic from only the currently attached host devices. What would be the most efficient way to configure MAC-level security on all these ports?
A – Visually verify the MAC addresses and then telnet to the switches to enter the switchport-port security mac-address command.
B – Have end users e-mail their MAC addresses. Telnet to the switch to enter the switchport-port security mac-address command.
C – Use the switchport port-security MAC address sticky command on all the switch ports that have end devices connected to them.
D – Use show mac-address-table to determine the addresses that are associated with each port and then enter the commands on each switch for MAC address port-security.
Answer: C
Explanation:
(Please read the explanation of question 1 to understand the use of the “switchport port-security MAC address sticky”)
A and C can be used, but instead of writing all the MAC addresses of the devices associated with each port, we can ask the switch to learn all the MAC addresses of the associated devices automatically by the “switchport port-security mac-address sticky” command which will save much work for the administrator.
Question 3
Refer to the exhibit. What can he concluded from the output of the debug command?
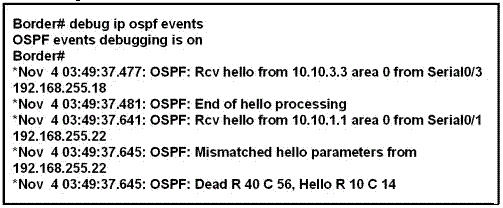
A – The output represents normal OSPF operation.
B – The interfaces of two OSPF routers connected to the Border router are in the same subnet.
C – The OSPF router connected to interface Serial0/1 has NOT formed a neighbor relationship with the Border router.
D – A router is connected to interface Serial0/3 of the Border router. The OSPF router ID of the connected router is the IP address of the connected interface.
Answer: C
Question 4
Refer to the exhibit. What does STATUS=ACTIVE refer to in the output of the show frame-relay pvc command?
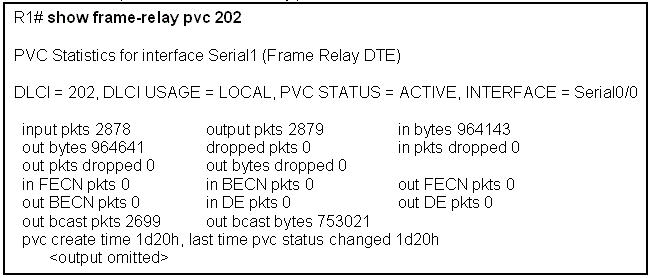
A – The PVC is experiencing congestion.
B – The Frame Relay switch is correctly programmed with the DLCI and is operational.
C – The router is actively broadcasting to establish a link to the Frame Relay switch.
D – The router is connected to the local Frame Relay switch, but not to the far end device.
Answer: B
Question 5
Refer to the graphic. Users on the Holyoke router are unable to access the intranet server attached to interface E0 of the Chicopee router. Inspection of the routing table of the Holyoke router shows that an entry for the Chicopee E0 network is missing. Which command will configure the Holyoke router with a path to the intranet server network?
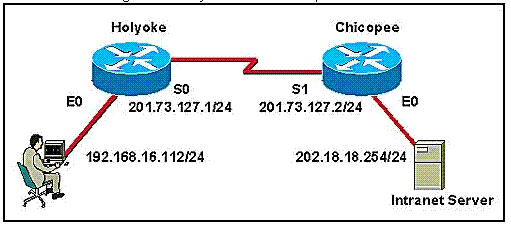
A – Holyoke(config)# ip host Chicopee 201.73.127.2
B – Holyoke(config)# ip host Chicopee 201.73.127.0 255.255.255.0
C – Holyoke(config)# ip network 202.18.38.0
D – Holyoke(config)# ip network 202.18.18.0 255.255.255.0
E – Holyoke(config)# ip route 202.18.18.0 255.255.255.0 201.73.127.2
F – Holyoke(config)# ip route 201.73.127.2 255.255.255.0 202.18.18.0
Answer: E
Question 6
Users have been complaining that their Frame Relay connection to the corporate site is very slow. The network administrator suspects that the link is overloaded. Based on the partial output of the Router#show frame relay pvc command shown in the graphic, which output value indicates to the local router that traffic sent to the corporate site is experiencing congestion?
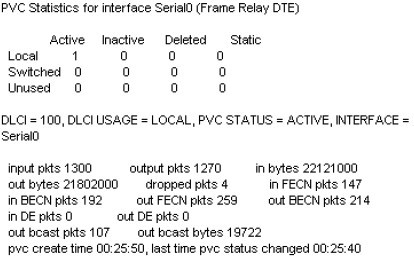
A.DLCI = 100
B.last time PVC status changed 00:25:40
C.in BECN packets 192
D.in FECN packets 147
E.in DE packets 0
Answer: C
Explanation
If one of the intermediate Frame Relay switches encounters congestion, it will set the BECN (Backward Error Congestion Notification) bit on packets being returned to the sending device and the FECN (Forward Error Congestion Notification) bit on the packets being sent to the receiving device.
A FECN tells the receiving device that the path is congested so that the upper layer protocols should expect some delay. The BECN tells the transmitting device that the Frame Relay network is congested and that it should “back off” to allow better throughput.
The DE (Discard Eligibility) bit is used to identify less important traffic that can be dropped during periods of congestion. DCE devices will discard frames with the DE bit set before discarding those that do not.
Question 7
Refer to the exhibit. Which of these statements correctly describes the state of the switch once the boot process has been completed?
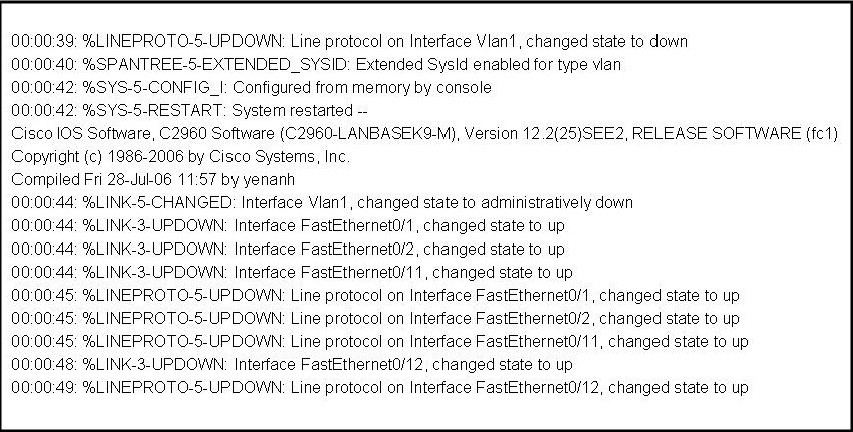
A. As FastEthernet0/12 will be the last to come up, it will be blocked by STP.
B. Remote access management of this switch will not be possible without configuration change.
C. More VLANs will need to be created for this switch.
D.The switch will need a different IOS code in order to support VLANs and STP.
Answer: B
Explanation
We don’t know the network topology so A is not correct.
A switch can operate without VLANs -> C is not correct.
This switch IOS supports VLAN because we can see VLAN 1 in the exhibit -> D is not correct.
In this case, VLAN 1 has been shutdown so we can’t remote access to this switch -> B is correct.
Hotspot
Here you will find answers to ICND 2 – Hotspot Questions
Question:
Refer to the topology. Using the information shown, answer the five questions shown on the Questions tab
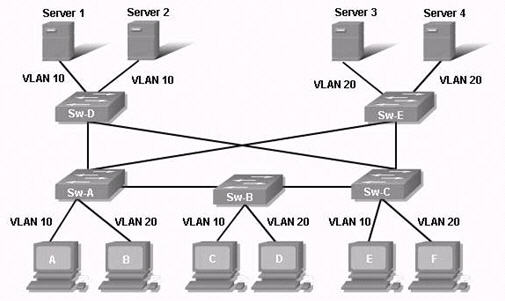
Question 1:
If most of the communication is between hosts and the servers, which switch is best as the root switch for VLAN 20?
A – Sw-A
B – Sw-B
C – Sw-C
D – Sw-D
E – Sw-E
Answer: E
Explanation:
Server 3 and Server 4 belong to VLAN 20 and are connected to Switch-E. If the question asks which switch is best for the whole network then the answer should be Switch-B because it is the most centralized switch on the network.
Question 2:
If Sw-E is the root for all VLANs, which of the following is a valid path from host A to Server 1?
A – Sw-A, Sw-D
B – Sw-A, Sw-E, Sw-D
C – Sw-A, Sw-B, Sw-C, Sw-D
D – Sw-A, Sw-E, Sw-C, Sw-D
E – Sw-A, Sw-E, Sw-A, Svv-D
Answer: D
Explanation:
All the traffic must go through root switch so the shortest path should be Sw-A -> Sw-E -> Sw-C -> Sw-D (notice that traffic can not go through Sw-A -> Sw-E and back to Sw-A again)
Question 3:
What technology helps prevent frames from looping continuously through this switched network?
A – ARP
B – VTP
C – STP
D – EIGRP
E – CSMA/CD
Answer: C
Question 4:
What, if anything, is required for communication to occur between the host C and Server 3?
A – DHCP
B – a router
C – nothing is required
D – trunk link between Sw-B and Sw-E
Answer: B
Explanation:
Since host C (VLAN 10) and Server 3 (VLAN 20) belong to different VLANs so we need a Layer 3 device (like a router) for inter-VLAN communication.
Question 5:
What type of link is needed between Sw-A and Sw-B so host C and host D can communicate through Sw-A to the servers?
A – trunk
B – access
C – multi-access
D – straight-through
Answer: A
Explanation:
Communication between different VLANs requires a trunk link to forward traffic normally.
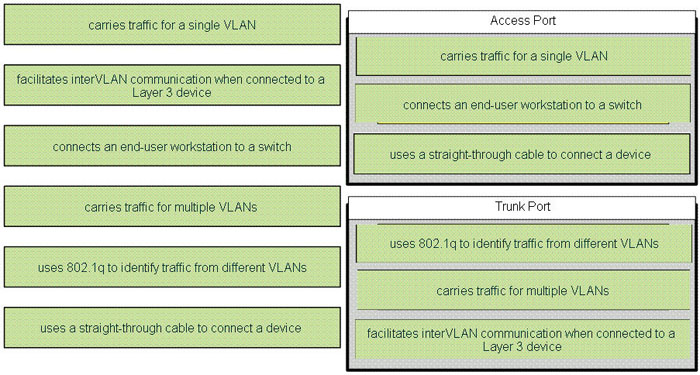
Question:
Drag the options on the left under the type of switch port that they describe on the right.
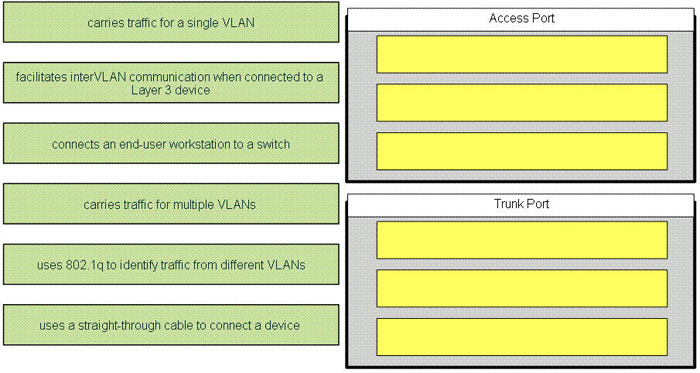
Answer:
Subnetting Questions
Here you will find answers to ICND 2 – Subnetting Questions
Note: If you are not sure about subnetting, please read my Subnetting tutorial.
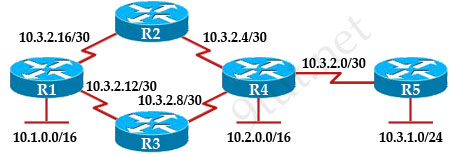
Question 1:
Refer to the exhibit. The lakeside Company has the internetwork in the exhibit. The Administrator would like to reduce the size of the routing table to the Central Router. Which partial routing table entry in the Central router represents a route summary that represents the LANS in Phoenix but no additional subnets?
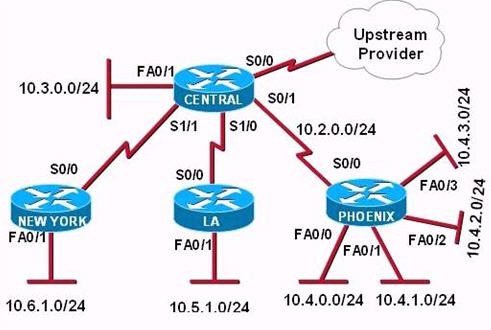
A – 10.0.0.0 /22 is subnetted, 1 subnet
D 10.0.0.0 [90/20514560] via 10.2.0.2 6w0d, serial 0/1
B – 10.0.0.0 /28 is subnetted, 1 subnet
D 10.2.0.0 [90/20514560] via 10.2.0.2 6w0d, serial 0/1
C – 10.0.0.0 /30 is subnetted, 1 subnet
D 10.2.2.0 [90/20514560] via 10.2.0.2 6w0d, serial 0/1
D – 10.0.0.0 /22 is subnetted, 1 subnet
D 10.4.0.0 [90/20514560] via 10.2.0.2 6w0d, serial 0/1
E – 10.0.0.0 /28 is subnetted, 1 subnet
D 10.4.4.0 [90/20514560] via 10.2.0.2 6w0d, serial 0/1
F – 10.0.0.0 /30 is subnetted, 1 subnet
D 10.4.4.4 [90/20514560] via 10.2.0.2 6w0d, serial 0/1
Answer: D
Question 2:
Refer to the exhibit. HostA cannot ping HostB. Assuming routing is properly configured. what could be the cause of this problem?
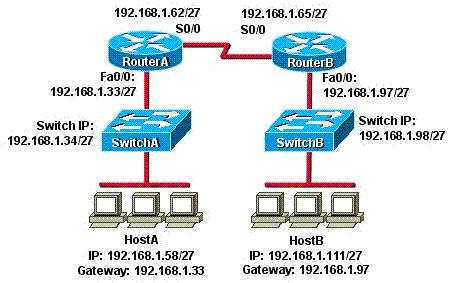
A – HostA is not on the same subnet as its default gateway.
B – The address of SwitchA is a subnet address.
C – The Fa0/0 interface on RouterA is on a subnet that can’t be used.
D – The serial interfaces of the routers are not on the same subnet.
E – The Fa0/0 interface on Routers is using a broadcast address.
Answer: D
Question 3:
Refer to the exhibit. The routers are running RIPv2. Which addressing scheme would satisfy the needs of this network yet waste fewest addresses?
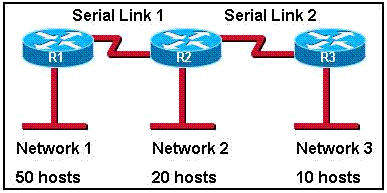
A – Network 1: 1 92.168.10.0/26
Network 2: 1 92.168.10.64/26
Network 3: 1 92.168.10.128/26
Serial link 1: 192.168.20.0/24
Serial link 2: 192.168.30.0/24
B – Network 1: 1 92.168.10.0/26
Network 2: 1 92.168.10.64/28
Network 3: 1 92.168.10.80/29
Serial link 1: 192.168.10.88/30
Serial link 2: 192.168.10.96/30
C – Network 1: 1 92.168.10.0/26
Network 2: 1 92.168.10.64/27
Network 3: 1 92.168.10.96/28
Serial link 1: 192.168.10.112/30
Serial link 2: 192.168.10.116/30
D – Network 1: 1 92.168.10.0/27
Network 2: 1 92.168.10.64/28
Network 3: 1 92.168.10.96/29
Serial link 1: 192.168.10.112/30
Serial link 2: 192.168.10.116/30
Answer: C
Drag and Drop Questions
Here you will find answers to ICND 2 – Drag And Drop Questions
Question 1
Two offices are displayed below
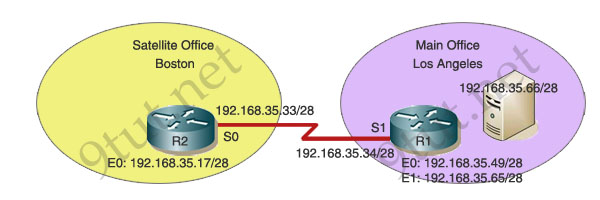
You work as a network technician at 9tut.net. Study the exhibit carefully. The company has a main office in Los Angeles and a satellite office in Boston. The offices are connected through two Cisco routers. The Boston satellite office is connected through the R2 router s0 interface to the Los Angeles office R1 router s1 interface. R1 has two local area networks. Boston users receive Internet access through the R1 router. Drag the boxes on the top to complete the goal on the left.
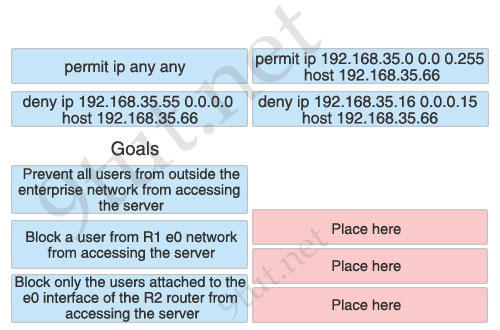
Answer:
1) Prevent all users from outside the enterprise network from accessing the server: permit ip 192.168.35.0 0.0 0.255 host 192.168.35.66
2) Block a user from R1 e0 network from accessing the server: deny ip 192.168.35.55 0.0.0.0 host 192.168.35.66
3) Block only the users attached to the e0 interface of the R2 router from accessing the server: deny ip 192.168.35.16 0.0.0.15 host 192.168.35.66
Question 2
You are configuring the 9tut.net office. In particular the host C, with the IP address 192.168.125.34/27, needs to be configured so that it cannot access hosts outside its own subnet. You decide to use the following command:
access-list 100 deny protocol address mask any
You are required to fill in the protocol, address, and mask in this command using the choices below:
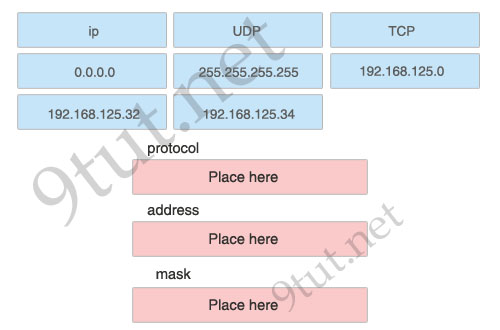
Answer:
1) protocol: ip
2) address: 192.168.125.34
3) mask: 0.0.0.0
Explanation
The syntax of extended access-list:
access-list 100-199 {permit|deny} {ip|tcp|udp|icmp} source source-mask [lt|gt|eq|neq] [source-port] destination dest-mask [lt|gt|eq|neq] [dest-port]
By telling the router to drop traffic originated from host C (source), we can guarantee that host C can just communicate with hosts inside its own subnet (because this kind of traffic does not need to pass the router and will not be prevented).
Question 3
Exhibit:
| Router# show interfaces s1/0 Seria11/0 is up, line protocol is up Hardware is CD2430 in sync mode Internet address is 192.168.0.10/30 MTU 1500 bytes, BW 128 Kbit, DLY 20000 usec, reliability 255/255, txload 1/255, rxload 1/255 Encapsulation PPP, LCP Open Open: CDPCP. IPCP, loopback not set Last input 00:00:00, output 00:00:00, output hang never Last clearing of “show interface” counters 4d21h |
Study the exhibit carefully. You need to match output lines in the exhibit with the proper OSI layer. One line will not be used.
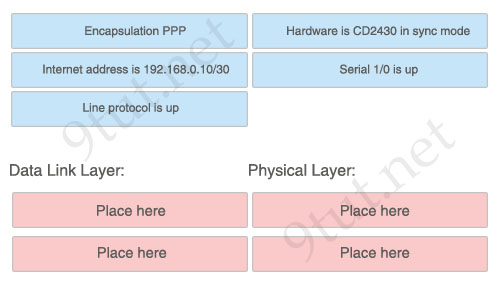
Answer:
Data Link Layer:
+ Encapsulation PPP
+ Line protocol is up
Physical Layer:
+ Serial 1/0 is up
+ Hardware is CD2430 in sync mode
Question 4
You work as a network administrator for your corporation, your boss is interested in switch ports. Match the options to the appropriate switch ports
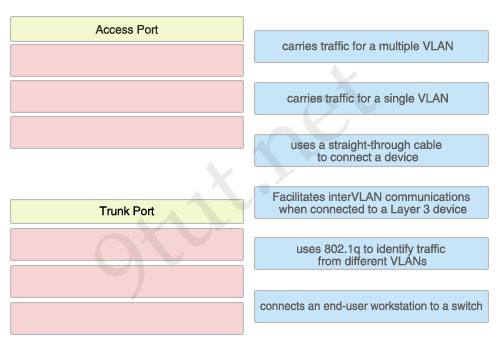
Answer:
Access Port:
+ carries traffic for a single VLAN
+ uses a straight-through cable to connect a device
+ connects an end-user workstation to a switch
Trunk Port:
+ carries traffic for a multiple VLAN
+ Facilitates interVLAN communications when connected to a Layer 3 device
+ uses 802.1q to identify traffic from different VLANs
Question 5
Below is the configuration of the R1 router:
R1(config)# ip route 0.0.0.0 0.0.0.0 192.168.1.1
R1(config)# ip route 10.1.0.0 255.255.255.0 192.168.2.2
R1(config)# ip route 10.1.0.0 255.255.0.0 192.168.3.3
Drag each destination IP address on the top to its correct next hop address at the bottom.
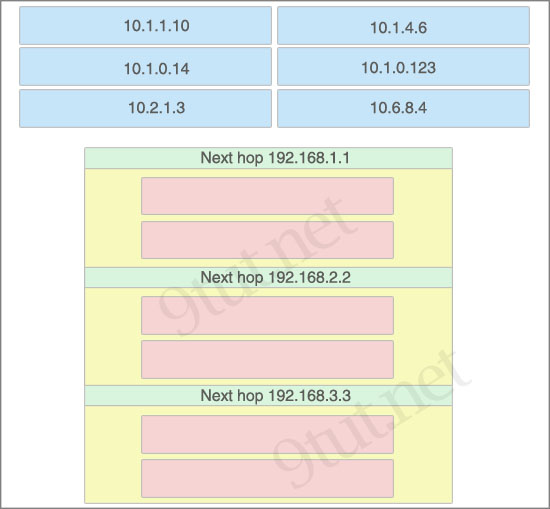
Answer:
Next hop 192.168.1.1:
+ 10.2.1.3
+ 10.6.8.4
Next hop 192.168.2.2:
+ 10.1.0.14
+ 10.1.0.123
Next hop 192.168.3.3:
+ 10.1.1.10
+ 10.1.4.6
Drag and Drop Questions 2
Here you will find answers to ICND 2 – Drag and Drop Questions Part 2
Question 1
Match the categories with the appropriate router output lines.
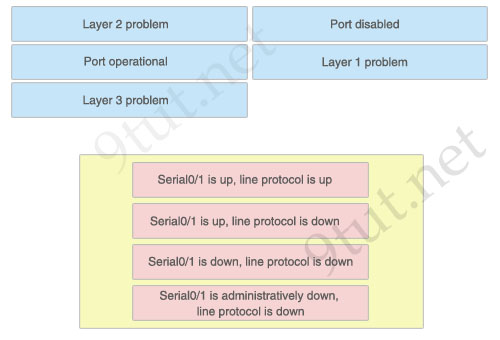
Answer:
1) Port operational: Serial0/1 is up, line protocol is up
2) Layer 2 problem: Serial0/1 is up, line protocol is down
3) Layer 1 problem: Serial0/1 is down, line protocol is down
4) Port disabled: Serial0/1 is administratively down, line protocol is down
Explanation:
A simple way to find out which layer is having problem is to remember this rule: “the first statement is for Layer 1, the last statement is for Layer 2 and if Layer 1 is down then surely Layer 2 will be down too”, so you have to check Layer 1 before checking Layer 2. For example, from the output “Serial0/1 is up, line protocol is down” we know that it is a layer 2 problem because the first statement (Serial0/1 is up) is good while the last statement (line protocol is down) is bad. For the statement “Serial0/1 is down, line protocol is down”, both layers are down so the problem belongs to Layer 1.
There is only one special case with the statement “…. is administratively down, line protocol is down”. In this case, we know that the port is currently disabled and shut down by the administrators.
Question 2
The above provides some descriptions, while the below provides some routing protocols. Drag the above items to the proper locations.
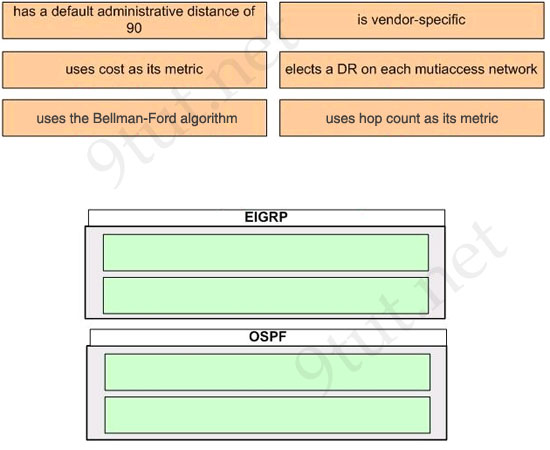
Answer:
EIGRP:
+ has a default administrative distance of 90
+ is vendor-specific
OSPF:
+ uses cost as its metric
+ elects a DR on each multiaccess network
Question 3
Drag the term on the left to its definition on the right (not all options are used)
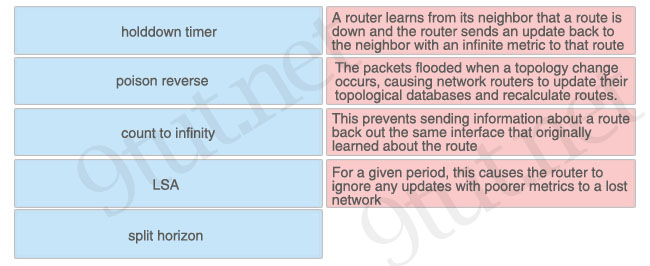
Answer:
+ poison reverse: A router learns from its neighbor that a route is down and the router sends an update back to the neighbor with an infinite metric to that route
+ LSA: The packets flooded when a topology change occurs, causing network routers to update their topological databases and recalculate routes
+ split horizon: This prevents sending information about a routeback out the same interface that originally learned about the route
+ holddown timer: For a given period, this causes the router to ignore any updates with poorer metrics to a lost network
Question 4
Drag the appropriate description to the correct locations
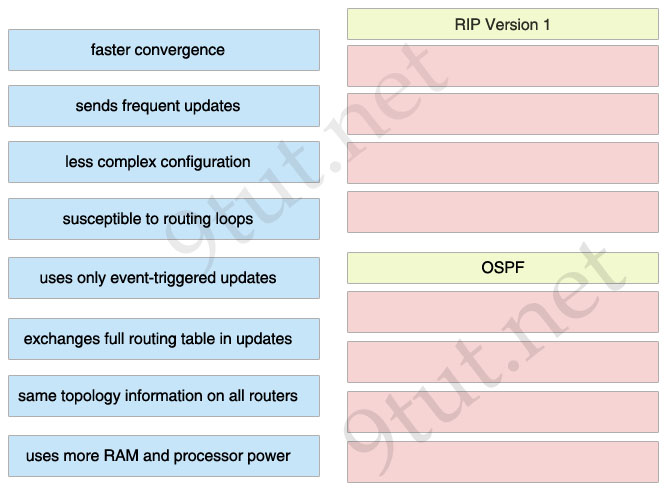
Answer:
RIP Version 1
+ sends frequent updates
+ less complex configuration
+ susceptible to routing loops
+ exchanges full routing table in updates
OSPF
+ faster convergence
+ uses only event-triggered updates
+ same topology information on all routers
+ uses more RAM and processor power
Question 5
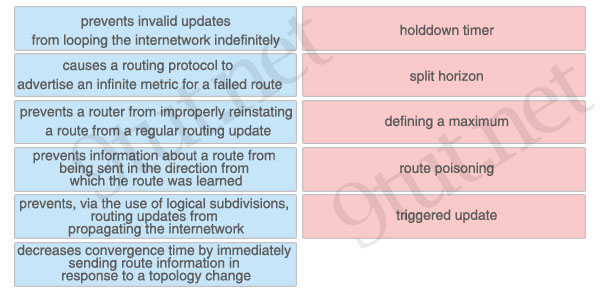
Answer:
+ holddown timer: prevents a router from improperly reinstating a route from a regular routing update
+ split horizon: prevents information about a route from being sent in the direction from which the route was learned
+ defining a maximum: prevents invalid updates from looping the internetwork indefinitely
+ route poisoning: causes a routing protocol to advertise an infinite metric for a failed route
+ triggered update: decreases convergence time by immediately sending route information in response to a topology change
Drag and Drop Questions 3
Here you will find answers to Drag and Drop Questions – Part 3
Question 1
Drag item on left to match item on right
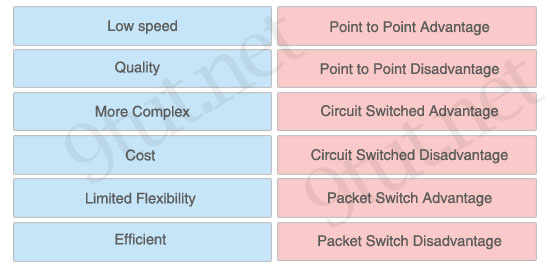
Answer:
+ Point to Point Advantage: Quality
+ Point to Point Disadvantage: Limited Flexibility
+ Circuit Switched Advantage: Cost
+ Circuit Switched Disadvantage: Low speed
+ Packet Switch Advantage: Efficient
+ Packet Switch Disadvantage: More Complex
Question 2
Place the Spanning-Tree Protocol port state on its functions (not all options on the left are used)
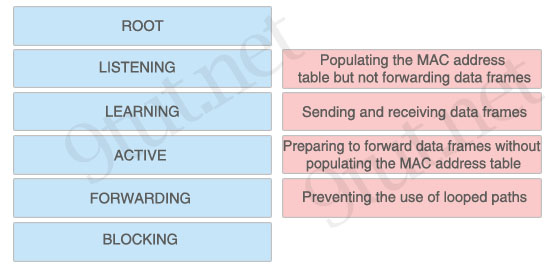
Answer:
+ Populating the MAC address table but not forwarding data frames: LEARNING
+ Sending and receiving data frames: FORWARDING
+ Preparing to forward data frames without populating the MAC address table: LISTENING
+ Preventing the use of looped paths: BLOCKING
Question 3
As a CCNA candidate, you need to know EIGRP very well.
Which tables of EIGRP route information are held in RAM and maintained through the use of hello and update packets?
Please choose two appropriate tables and drag the items to the proper locations.
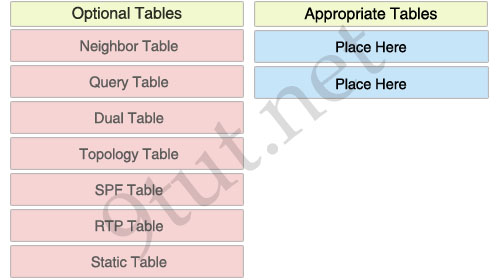
Answer:
Neighbor Table
Topology Table
Miscellaneous Questions
Here you will find answers to Miscellaneous Questions
Question 1
For what two purposes does the Ethernet protocol use physical addresses? (Choose two)
A. to uniquely identify devices at Layer 2
B. to allow communication with devices on a different network
C. to differentiate a Layer 2 frame from a Layer 3 packet
D. to establish a priority system to determine which device gets to transmit first
E. to allow communication between different devices on the same network
F. to allow detection of a remote device when its physical address is unknown
Answer: A E
Question 2
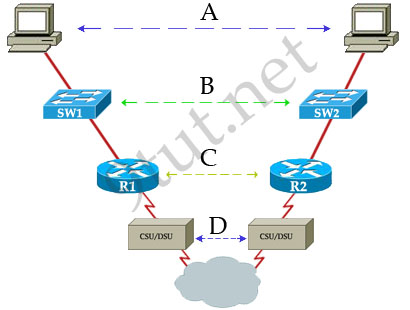
In the communication between host 1 and host 2 over the point-to-point WAN, which protocol or technology is represented by dashed line A?
A. IP
B. T1
C. ppp
D. IEEE 802.3
Answer: A
Question 3
What three pieces of information can be used in an extended access list to filter traffic? (Choose three)
A. protocol
B. VLAN number
C. TCP or UDP port numbers
D. source switch port number
E. source IP address and destination IP address
F. source MAC address and destination MAC address
Answer: A C E
Question 4
For security reasons, the network administrator needs to prevent pings into the corporate networks from hosts outside the internetwork. Which protocol should be blocked with access control lists?
A. IP
B. ICMP
C. TCP
D. UDP
Answer: B
Question 5
An administrator attempts a traceroute but receives a “Destination Unreachable” message. Which protocol is responsible for that message?
A. RARP
B. RUDP
C. ICMP
D. SNMP
Answer: C
Question 6
What are two characteristics of Frame Relay point-to-point subinterfaces? (Choose two)
A. They create split-horizon issues.
B. They require a unique subnet within a routing domain.
C. They emulate leased lines.
D. They are ideal for full-mesh topologies.
E. They require the use of NBMA options when using OSPF.
Answer: B C
Question 7
From EIGRP, OSPF, and a static route, a router learns about a remote network.
Assuming that default administrative distance is used by all routing protocols, to forward data to the remote network, which route will the router use?
A. The router will use the OSPF route.
B. The router will use the EIGRP route.
C. The router will use the static route.
D. The router will load balance and use all three routes.
Answer: C
Question 8

To connect the autonomous systems, which routing protocol should be used?
A. RIP
B. OSPF
C. BGP
D. EIGRP
Answer: C
Share your ICND2 Experience
Please share with us your experience after taking the exam ICND2, your materials, the way you learned, your recommendations…